Hello Friends in this article i am gone to share Coursera Course: IBM Cybersecurity Analyst Professional Certificate Assessment Exam Answers 2023 with you..
Enroll Link: IBM Cybersecurity Analyst
IBM Cybersecurity Analyst Professional
Certificate Assessment Exam Quiz Answers | 2023
Question 1)
Which of these is the best definition of a security risk?
- Any potential danger that is associated with the exploitation of a vulnerability
- A weakness in a system
- An instance of being exposed to losses
- The likelihood of a threat source exploiting a vulnerability
Question 2)
Fancy Bears and Anonymous are examples of what?
- Types of malware
- Hacking organizations
- Cryptographic cyphers
- Popular computer security blogs
Question 3
How would you classify a piece of malicious code that can replicate itself and spread to new systems?
- A virus
- A worm
- Spyware
- A Trojan Horse
Question 4)
To engage in packet sniffing, you must implement promiscuous mode on which device?
- An Intrusion Detection System (IDS)
A Promiscuous Gateway- A sniffing router
- A network card
Question 5)
Which mechanism would help assure the integrity of a message, but not do much to assure confidentiality or availability.
- Encrypting
- Hashing
- Mirroring
- Audit logs
Question 6)
A company wants to prevent employees from wasting time on social media sites. To accomplish this, a document forbidding use of these sites while at work is written and circulated and then the firewalls are updated to block access to Facebook, Twitter and other popular sites. Which two (2) types of security controls has the company just implemented? (Select 2)
- Administrative
- Technical
- Physical
- Operational
Question 7)
Which factor contributes most to the strength of an encryption system?
- How many people have access to your public key
- The length of the encryption key used
- The secrecy of the encryption algorithm used
- The number of private keys used by the system
Question 8)
What is an advantage asymmetric key encryption has over symmetric key encryption?
- Asymmetric keys can be exchanged more securely than symmetric keys
- Asymmetric key encryption is faster than symmetric key encryption
- Asymmetric key encryption is harder to break than symmetric key encryption
- Asymmetric key encryption provides better security against Man-in-the-middle attacks than is possible with symmetric key encryption
Question 9)
Which position is in charge of testing the security and effectiveness of computer information systems?
- Information Security Analyst
- Information Security Architect
- Chief Information Officer (CIO)
- Information Security Auditor
Question 10)
Which position conducts information security investigations for organizations to identify threats that could compromise the organization?
- Vulnerability Assessor
- Information Security Architect
- Information Security Auditor
- Information Security Analyst
Question 11)
Which three (3) are considered best practices, baselines or frameworks? (Select 3)
- IS027000 series
- ITIL
- COBIT
- HIPAA
- GDPR
Question 12)
Alice sends a message to Bob that is intercepted by Trudy. Which scenario describes an availabilityviolation?
- Trudy cannot read it because it is encrypted but allows it to be delivered to Bob in its original form
- Trudy changes the message and then forwards it on
- Trudy deletes the message without forwarding it
- Trudy reads the message
Question 13)
In cybersecurity, Authenticity is defined as what?
- The property of being genuine and verifiable
- Being able to map an action to an identity
- The first or original copy of a document or message
- Being able to apply financial management to a process
Question 14)
Multifactor authentication (MFA) requires more than one authentication method to be used before identity is authenticated. Which three (3) are authentication methods? (Select 3)
- Something a person is
- Something a person knows
- Somewhere a person is located
- Something a person has
Question 15)
The encryption and protocols used to prevent unauthorized access to data are examples of which type of access control?
- Technical
- Physical
- Administrative
- Embedded
Question 16)
A Windows 10 user has 10 files with exactly the same name. Which statement must be true for these files?
- The files may be in the same directory
- The files must be on different hard drives
- The files may be on the same hard drive but must be in different partitions
- The files must be in different directories
Question 17)
In a Linux file system, which files are contained in the \bin folder?
- Configuration files such as (stab and inittab
- Executable files such as grep and ping
- Directories such as /home and /usr
- All user binary files, their libraries and headers
Question 18)
A small and underfunded startup company should consider using which type of cloud first?
- Public cloud
- Hybrid cloud
- Private cloud
- Universal cloud
Question 19)
Consolidating and virtualizing workloads should be done when?
- After moving the workloads to the cloud but before they are open to users
- Before moving the workloads to the cloud
- It does not matter; these steps require approximately the same amount of work no matter when you elect to do them radually as you generate usage metrics
Question 20)
Which regulation contains the security rule that requires all covered entities to maintain reasonable and appropriate administrative, technical, and physical safeguards for protecting electronic protected health information (e-PHI)?
- PCI-DSS
- HIPAA
- 15027000 series
- HIST 800-53A
- GDPR
Question 21)
Which two (2) of the following attack types target endpoints?
- Denial of Service (DoS)
- SQL Injection
- Spear Phishing
- Ad Network
Question 22)
A good Endpoint Detection and Response system (EDR) should have which three (3) of these capabilities?
- Manage thousands of devices at once
- Automatically quarantine noncompliant endpoints
- Manage encryption keys for each endpoint
- Deploying devices with network configurations
Question 23)
Granting access to a user account only those privileges necessary to perform its intended functions is known as what?
- The principle of least privileges
- Role Based Access Control (RBAC)
- The principle of unified access control
- The principle of top-down control
Question 24)
The Windows Security App available in Windows 10 provides uses with which of the following protections?
- Virus and threat protection
- Firewall and network protection
- Family options (parental controls)
- All of the above
Question 25)
Symmetric key encryption by itself ensures which of the following?
- Confidentiality and Integrity
- Confidentiality only
- Confidentiality and Availability
- Confidentiality, Integrity and Availability
Question 26)
Which of the following practices helps assure the best results when implementing encryption?
- Choose a reliable and proven published algorithm
- Develop a unique cryptographic algorithm for your organization and keep them secret
- Change the cryptographic algorithm used monthly
- Hard-code encryption keys into your applications to assure consistent use
Question 27)
Which of the following statements about hashing is True?
- Hashing uses algorithms that are known as “one-way” functions
- A weakness of hashing is that the hash is proportional in length to the original message
- The original message can be retrieved from the hash if you have the encryption key
- If you have two hashes that differ only by a single character, you can infer thatthe original messages also differed very little
Question 28)
Which statement about encryption is True for data in use.
- Data in active memory registers are not at risk of being stolen
- Data should always be kept encrypted since modern CPUs are fully capable of operating directly on encrypted data
- It is vulnerable to theft and should be decrypted only for the briefest possible time while it is being operated on
- Short of orchestrating a memory dump from a system crash, there is no practical way for ma lwa re to get at the data being processed, so dump logs are your only real concern
Question 29)
For added security you decide to protect your network by conducting both a stateless and stateful inspection of incoming packets. How can this be done?
- Install a stateful firewall only These advanced devices inspect everything a stateless firewall inspects in addition to state related factors
- You must install 2 firewall Hs in series, so all packets pass through the stateless firewall first and then the stateless fi rewa IL
- This cannot be done The network administrator must choose to run a given network segment in either stateful or stateless mode, and then select the corresponding firewall type
- Install a single firewall that is capable of conducting both stateless and stateful inspections
Question 30)
Which statement best describes configuring a NAT router to use dynamic mapping?
- The organization will need as many registered IP addresses as it has computers that need Internet access
- Unregistered IP addresses are mapped to registered IP addresses as they are needed
- Many registered IP addresses are mapped to a single registered IP address using different port numbers
- The NAT router uses each computer’s IP address for both internal and external communication
Question 31)
If a computer needs to send a message to a system that is part of the local network, where does it send the message?
- To the system’s IP address
- To the system’s domain name
- The network’s DNS server address
- To the system’s MAC address
Question 32)
In IPv4, how many of the 4 octets are used to define the network portion of the address in a Class B network?
- 1
- 2
- 3
- 4
Question 33)
What is the primary difference between the IPv4 and I Pv6 addressing schema?
- IPv6 allows for billions of times as many possible IP addresses
- IPv6 is a simple version update to IPv4 with numerous bugs fixed
- IPv6 is significantly faster than IPv4
- IPv6 is used only for IOT devices
Question 34)
Which type of firewall understands which session a packet belongs to and analyzes it accordingly?
- An Advanced Firewall (AFW)
- A Connection Firewall (CFW)
- A Next Generation Firewall (NGFW)
- A Session Firewall (SFW)
Question 35)
If you have to rely upon metadata to work with the data at hand, you are probably working with which type of data?
- Unstructured data
- Meta-structured data
- Structured data
- Semi-structured data
Question 36)
In reviewing the security logs for a company’s headquarters in New York City, which of these activities should not raise much of a security concern?
- Each night one headquarters employee logs into his account from an ISP in China
- One evening an employee logs in from home and downloads all of the files associated with the new product he is working on
- An employee has started logging in from home for an hour or so during the last 2 weeks of each quarter
- A recently hired data scientist in the Medical Analytics department has repeatedly attempted to access the corporate financial database
Question 37)
Poor user input sanitation and unsafe execution of OS commands leaves a system vulnerable to which form of attack?
- Denial of Service (DoS)
- DLL Hijacking
- SQL Injection
- OS Command Injection
Question 38)
An employee calls the IT Helpdesk and admits that maybe, just possibly, the links in the email he clicked on this morning were not from the real Lottery Commission. What is the first thing you should tell the employee to do?
- Run an antivirus scan
- Run a Port scan
- Run a vulnerability scan
- Start searching his hard drive for unusual files or folders
Question 39)
If a penetration test calls for you to create a diagram of the target network including the identity of hosts and servers as well as a list of open ports and published services, which tool would be the best fit for this task?
- Metasploit
- John the Ripper
- Wireshark
- Nmap
Question 40)
Which Incident Response Team model describes a team that runs all incident response activities for a company?
- Control
- Coordinating
- Distributed
- Central
Question 41)
Which of the following would be considered an incident precursor?
- Application logs indicating multiple failed login attempts from an unfamiliar remote system
- An announced threat against your organization by a hactivist group
- An alert from your antivirus software indicating it had detected malware on your system
- An email administrator seeing a large number of emails with suspicious content
Question 42)
Forensic analysis should always be conducted on a copy of the original data. Which two (2) types of copying are appropriate for getting data from a laptop acquired from a terminated employee, if you suspect he has deleted
incriminating files? (Select 2)
- An incremental backup
- A disk-to-file backup
- A disk-to-disk backup
- A logical backup
Question 43)
Which three (3) are common obstacles faced when trying to examine forensic data? (Select 3)
- Acquiring data from the crime scene
- Selecting the right tools to help filter and exclude irrelevant data
- Bypassing controls such as passwords
- Finding the relevant files among the hundreds of thousands found on most hard drives
Question 44)
PowerShell is a configuration management framework for which operating system?
- Windows
- Linux
- UNIX
- Mac OS X
Question 45)
Which two (2) statements about Python are true? (Select 2)
- Python code is considered very readable by novice programmers
- Python code is written at a very low level to better integrate with operating system functions
- Python is not considered portable, running only on Linux and Windows machines
- Python code is considered easy to debug compared with other popular programming languages
Question 46)
What is the largest number that will be printed during the execution of this Python while loop?
while (i<10):
print(i)
i=i+1
Answer: 9
Question 47)
What will be printed by the following block of Python code?
def Add5(in)
out=in+5
return out
print(Add5(10))
- 10
- 5
- 15
- AddS(10)
Question 48)
Which country had the highest average cost per breach in 2018 at $8.19M
- Russia
- Japan
- United Kingdom
- Germany
- United States
- China
Question 49)
True or False. An organization’s security immune system should be integrated with outside organizations, including vendors and other third-parties.
- True
- False
Question 50)
A professor is not allowed to change a student’s final grade after she submits it without completing a special form to explain the circumstances that necessitated the change. This additional step supports which aspect of the CIA Triad?
- Confidentiality
- Availability
- Authorization
- Integrity
Question 51)
True or False. For iOS and Android mobile devices, users must interact with the operating system only through a series of applications, but not directly.
- True
- False
Question 52)
True or False. Internal attacks from trusted employees represents every bit as significant a threat as external attacks from professional cyber criminals.
- True
- False
Question 53)
Which type of scan is quieter than other TCP scans and can get around firewalls, but can be detected with newer IDSs?
- UM, portscan
- TCP/Half Open Scan (aka a SYN scan)
- Stealth scan
- TCP Conned
- Ping (IC MP Echo Request)
Question 54)
What organization managers the assignment and registration of port numbers?
- Internet Port Assignment Authority (IPAA)
- Internet Engineering Task Force (IETF)
- Internet Assigned Numbers Authority (IANA)
- Internet Architecture Board (IAB)
Question 55)
Which phase of DevSecOps would contain the activities Internal/External testing, Continuous assurance, and Compliance checking?
- Release, deploy &decommission
- Operate & monitor
- Plan
- Test
- Code & build
Question 56)
You calculate that there is a 2% probability that a cybercriminal will be able to steal credit card numbers from your online storefront, which will result in $10M in losses to your company. What have you just determined?
- A vector
- A vulnerability
- A threat
- A risk
Question 57)
Which of the OWASP Top 10 Application Security Risks would be occur when there are no safeguards against a user being allowed to execute HTML or JavaScript in the user’s browser that can hijack sessions.
- Security misconfiguration
- Insufficient logging and monitoring
- Cross-site scripting
- Insecure deserialization
Question 58)
Solution architectures often contain diagrams like the one below. What does this diagram show?
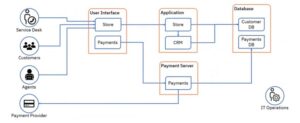
- Enterprise architecture
- Functional components and data flow
- Architecture overview
- External context and boundary diagram
Question 59)
SIEM license costs are typically calculated based upon which two (2) factors? (Select 2)
- Flows per minute (FPM)
- The MSU capacity of the system running the SIEM
- Events per second (EPS)
- Number of users with access to the SIEM
Question 60)
The partnership between security analysts and technology can be said to be grouped into 3 domains, human expertise, security analytics and artificial intelligence. The human expertise domain would contain which three (3) of these topics?
- Pattern identification
- Anomaly detection
- Machine Learning
- Morals
- Dilemmas
- Abstraction
Question 61)
True or False. Thorough reconnaissance is an important step in developing an effective cyber kill chain.
- True
- False
Question 62)
The cyber hunting team and the SOC analysts are informally referred to as the ____ and ____ teams, respectively.
- Red, Blue
- Blue Red
- Attack, Defense
- Visitors, Home
Question 63)
True or False. A large company has a data breach involving the theft of employee personnel records but no customer data of any kind. Since no external data was involved, the company does not have to report the breach to law enforcement.
- True
- False
Question 64)
True or False. Communications of a data breach should be handled by a team composed of members of the IR team, legal personnel and public relations.
- True
- False
Question 65)
You are the CEO of a large tech company and have just received an angry email that looks like it came from one of your biggest customers. The email says your company is overbilling the customer and asks that you examine the attached invoice. You do but find it blank, so you reply politely to the sender asking for more details. You never hear back, but a week later your security team tells you that your credentials have been used to access and exfiltrate large amounts of company financial data. What kind of attack did you fall victim to?
- A shark attack
- As a whale attack
- As a phishing attack
- A fly phishing attack
Question 66)
Which three (3) of these are PCI-DSS requirements for any company handling, processing or transmitting credit card data? (Select 3)
- All employees with direct access to cardholder data must change their passwords monthly
- Assign a unique ID to each person with computer access
- Restrict physical access to cardholder data
- Restrict access to cardholder data by business need-to-know
Question 67)
Stolen credit card numbers are sold to brokers who resell them to carders who use them to buy prepaid credit cards that are then used to buy gift cards that will be used to buy merchandise that is shipped to a reshipper who sends it on to its final destination before it is sold for profit.
Why is such a complex process used instead of simply using the stolen numbers to buy the products that are desired?
- It is easierto get approval to use a credit card to purchase a prepaid credit card than to it is to purchase merchandise
- To make the end-to-end transaction very difficult to follow
- Because stolen cards can rarely be used directly to purchase merchandise
- If done quickly, there is a multiplying effect in play. The stolen credit card can be used to buy 3 or4 prepaid cards each valued at the credit limit of the original card. The same is true for using each prepaid card to buy multiple gift cards and each gift card to buy more merchandise than its face value
Question 68)
According to a 2019 Ponemon study, what percent of consumers indicated they would be willing to pay more for a product or service from a provider with better security?
- 12%
- 24%
- 52%
- 92%
Question 69)
You are looking very hard on the web for the lowest mortgage interest load you can find and you come across a rate that is so low it could not possibly be true. You check out the site to see what the terms are and quickly find you are the victim of a ransomware attack. What was the likely attack vector used by the bad actors?
- Phishing
- Remote Desktop Protocol (RDP)
- Malicious Links
- Software Vulnerabilities
Question 70)
Very provocative articles that come up in news feeds or Google searches are sometimes called “click-bait”. These articles often tempt you to link to other sites that can be infected with malware. What attack vector is used by these click-bait sites to get you to go to the really bad sites?
- Phishing
- Software Vulnerabilities
- Malicious Links
- Remote Desktop Protocol (RDP)
For More Question Go to this Links
IBM Cybersecurity Analyst Practice Quiz Answers